What businesses can learn from armadillos, seahorses, and zebras.  By GilesWitherspoon-BoydHackers are a lot like predators in the wild. After finding an unsuspecting animal, nature’s hunters test their victim for weaknesses before taking it down. Just like nature’s hunters, hackers aren’t looking for a challenge. They’re looking for an easy target. Unfortunately, it seems as if hackers are always one step ahead. So how do you avoid becoming dinner? Take a clue from nature. It’s all about defense mechanisms.
By GilesWitherspoon-BoydHackers are a lot like predators in the wild. After finding an unsuspecting animal, nature’s hunters test their victim for weaknesses before taking it down. Just like nature’s hunters, hackers aren’t looking for a challenge. They’re looking for an easy target. Unfortunately, it seems as if hackers are always one step ahead. So how do you avoid becoming dinner? Take a clue from nature. It’s all about defense mechanisms.![]() Tweet1. The LookoutDwarf mongoose post sentries that stand on their hind legs to watch for birds (their main predator). When a bird is sighted, they send a warning call to others and run to safety.
Tweet1. The LookoutDwarf mongoose post sentries that stand on their hind legs to watch for birds (their main predator). When a bird is sighted, they send a warning call to others and run to safety.  Just like the sentries that stand outside dwarf mongoose burrows, businesses have file integrity monitoring software, or log monitoring. Log monitoring systems collect and store logs. Logs are user actions inside an operating system (e.g., renaming a file, opening an application). Some systems have a real-time reporting system (like the dwarf mongoose call) that alerts you via email or text of suspicious activity.
Just like the sentries that stand outside dwarf mongoose burrows, businesses have file integrity monitoring software, or log monitoring. Log monitoring systems collect and store logs. Logs are user actions inside an operating system (e.g., renaming a file, opening an application). Some systems have a real-time reporting system (like the dwarf mongoose call) that alerts you via email or text of suspicious activity. Reviewing logs on a regular basis helps identify malicious attacks on your system. According to the PCI DSS, businesses are supposed to have 12 months of logs stored, with 3 months readily available. Systems that have log monitoring capabilities include operating systems, Internet browsers, point of sale systems, firewalls, and intrusion detection systems (IDS). Some systems do not automatically enable logging (e.g., Windows XP out of the box has logging turned off).2. The UpgraderIn the animal kingdom, bigger is often better. A larger, stronger set of antlers helps white-tailed bucks successfully battle other males during mating season. Every year, they shed their antlers to grow bigger ones for next season.
Reviewing logs on a regular basis helps identify malicious attacks on your system. According to the PCI DSS, businesses are supposed to have 12 months of logs stored, with 3 months readily available. Systems that have log monitoring capabilities include operating systems, Internet browsers, point of sale systems, firewalls, and intrusion detection systems (IDS). Some systems do not automatically enable logging (e.g., Windows XP out of the box has logging turned off).2. The UpgraderIn the animal kingdom, bigger is often better. A larger, stronger set of antlers helps white-tailed bucks successfully battle other males during mating season. Every year, they shed their antlers to grow bigger ones for next season. Just like deer upgrade their antlers, you should be regularly updating your software to make sure it has the most up to date patches for security vulnerabilities. Devices and software that should be regularly updated include: operating systems, anti-virus software, POS terminals, firewalls, intrusion detection systems (IDS), mobile devices, Internet browsers, app software, and more. 3. The HiderEveryone knows that chameleons change colors to match their environment and allow attackers to pass them over. But so do seahorses, cuttlefish, octopus, and dozens of other animals. Changing colors is a great defense mechanism for animals without strength or stamina.
Just like deer upgrade their antlers, you should be regularly updating your software to make sure it has the most up to date patches for security vulnerabilities. Devices and software that should be regularly updated include: operating systems, anti-virus software, POS terminals, firewalls, intrusion detection systems (IDS), mobile devices, Internet browsers, app software, and more. 3. The HiderEveryone knows that chameleons change colors to match their environment and allow attackers to pass them over. But so do seahorses, cuttlefish, octopus, and dozens of other animals. Changing colors is a great defense mechanism for animals without strength or stamina.  Just like these animals hide their vulnerable bodies, it’s important for you to hide what’s most important to your business: customer credit card data. Did you know 63% of businesses store unencrypted card data? If a credit card isn’t encrypted, it’s completely exposed on your network, with no camouflage protecting it from predators snooping around. Encryption is the best way to hide data, but by finding and deleting unnecessary data, you have nothing to hide. After all, hackers can’t steal what isn’t there.4. The TankSome animals undergo structural changes to protect their bodies from predators. Take the thick skin of the armadillo. It’s made of an armor-like substance and can roll into an indestructible ball if the armadillo is threatened.
Just like these animals hide their vulnerable bodies, it’s important for you to hide what’s most important to your business: customer credit card data. Did you know 63% of businesses store unencrypted card data? If a credit card isn’t encrypted, it’s completely exposed on your network, with no camouflage protecting it from predators snooping around. Encryption is the best way to hide data, but by finding and deleting unnecessary data, you have nothing to hide. After all, hackers can’t steal what isn’t there.4. The TankSome animals undergo structural changes to protect their bodies from predators. Take the thick skin of the armadillo. It’s made of an armor-like substance and can roll into an indestructible ball if the armadillo is threatened.  The structural change businesses should use to protect their business is a firewall, both software and hardware. Like a security guard, properly configured firewalls control what goes in, and what comes out of your business. SEE ALSO: How Does a Firewall Protect a Business?5. The TricksterZebras use their striped pattern as an optical illusion to confuse predators. Because each zebra has a unique striped pattern, it’s difficult for predators to single one out.
The structural change businesses should use to protect their business is a firewall, both software and hardware. Like a security guard, properly configured firewalls control what goes in, and what comes out of your business. SEE ALSO: How Does a Firewall Protect a Business?5. The TricksterZebras use their striped pattern as an optical illusion to confuse predators. Because each zebra has a unique striped pattern, it’s difficult for predators to single one out.  Businesses should apply the zebra strategy to passwords. Each network, device, and user should have a unique username and password. In addition, make sure each of those unique passwords are difficult to guess. The easiest way to create a tricky password is by creating a passphrase. Anyone love Corey Hart’s 1980’s hit, “I wear my sunglasses at night”? If you do, good. If not, too bad. It’s turning into my example passphrase. To create a complex passphrase, take the first letter of each word, and substitute special characters/numbers where you can. I wear my sunglasses at night –> Iwmsg@n1980!6. The TeacherIn a recent study on lion cubs, researchers learned lions aren’t born with a natural fear of humans. They learn it from their mothers and the rest of the pride. For a species like lions to continue to prosper, their defense mechanism is to quickly teach their young to avoid other species that could harm them…aka humans.
Businesses should apply the zebra strategy to passwords. Each network, device, and user should have a unique username and password. In addition, make sure each of those unique passwords are difficult to guess. The easiest way to create a tricky password is by creating a passphrase. Anyone love Corey Hart’s 1980’s hit, “I wear my sunglasses at night”? If you do, good. If not, too bad. It’s turning into my example passphrase. To create a complex passphrase, take the first letter of each word, and substitute special characters/numbers where you can. I wear my sunglasses at night –> Iwmsg@n1980!6. The TeacherIn a recent study on lion cubs, researchers learned lions aren’t born with a natural fear of humans. They learn it from their mothers and the rest of the pride. For a species like lions to continue to prosper, their defense mechanism is to quickly teach their young to avoid other species that could harm them…aka humans. Training is such a crucial security strategy. I can’t count how many compromises could have been prevented if staff were simply educated on the dangers of hackers. Business owners, IT staff, and managers must train staff members on physical security, phishing, passwords, policies, etc. so they can take the necessary steps to protect the business. 7. The IntimidatorHave you ever seen a lizard do a pushup? Those lizards are showing their strength to intimidate predators. Do you know the reason gazelles jump so high? It’s to demonstrate their ability to outrun pursuers. You know those lizards that flare extra skin around their neck when they are threatened? By doing so, they appear larger and more threatening to those that may try to eat them.
Training is such a crucial security strategy. I can’t count how many compromises could have been prevented if staff were simply educated on the dangers of hackers. Business owners, IT staff, and managers must train staff members on physical security, phishing, passwords, policies, etc. so they can take the necessary steps to protect the business. 7. The IntimidatorHave you ever seen a lizard do a pushup? Those lizards are showing their strength to intimidate predators. Do you know the reason gazelles jump so high? It’s to demonstrate their ability to outrun pursuers. You know those lizards that flare extra skin around their neck when they are threatened? By doing so, they appear larger and more threatening to those that may try to eat them. With nothing but their body language, animals signal to predators, “Attacking me is not worth your time. So don’t even try.”While it’s difficult to show to a hacker just how strong your business security posture is, the best way all-around way to maintain solid security is by complying with the PCI DSS. That means going through each section of the Self-Assessment Questionnaire (SAQ) and ensuring your organization’s compliance with all the requirements.SEE ALSO: Which PCI SAQ is Right for My Business?If you liked this post, please share!
With nothing but their body language, animals signal to predators, “Attacking me is not worth your time. So don’t even try.”While it’s difficult to show to a hacker just how strong your business security posture is, the best way all-around way to maintain solid security is by complying with the PCI DSS. That means going through each section of the Self-Assessment Questionnaire (SAQ) and ensuring your organization’s compliance with all the requirements.SEE ALSO: Which PCI SAQ is Right for My Business?If you liked this post, please share!![]() Giles Witherspoon-Boyd (PCIP) is Enterprise Account Manager at SecurityMetrics and assists businesses in defining their PCI DSS scope. Follow him on Twitter and check out his other blog posts.
Giles Witherspoon-Boyd (PCIP) is Enterprise Account Manager at SecurityMetrics and assists businesses in defining their PCI DSS scope. Follow him on Twitter and check out his other blog posts.
Social Engineering – It’s OK To Be a Little Paranoid
After all, gullible employees lead to security breaches.  By: Brand BarneyHumans want to trust other humans. If I struck up a conversation with a gentleman in a suit at the bus stop who explained his life story, why would I distrust him? We all have a natural tendency to believe what trustworthy-looking people tell us. And that’s what gets us in trouble.
By: Brand BarneyHumans want to trust other humans. If I struck up a conversation with a gentleman in a suit at the bus stop who explained his life story, why would I distrust him? We all have a natural tendency to believe what trustworthy-looking people tell us. And that’s what gets us in trouble.![]() Tweet
Tweet What is social engineering?Social engineering is a way of manipulating people socially so that they trust the social engineer and eventually provide some sort of useable data. For instance, instead of trying to find software vulnerabilities to exploit for sensitive data, a social engineer might try to trick someone into divulging an administrative password without realizing it.Have you ever seen the crime drama Catch Me If You Can? Frank Abagnale, the main character, is a master of social engineering. He convinces people he’s an airline pilot, doctor, and attorney by forging documents and acting like he belongs. The scary thing is, it’s a true story.What’s the problem with social engineering?
What is social engineering?Social engineering is a way of manipulating people socially so that they trust the social engineer and eventually provide some sort of useable data. For instance, instead of trying to find software vulnerabilities to exploit for sensitive data, a social engineer might try to trick someone into divulging an administrative password without realizing it.Have you ever seen the crime drama Catch Me If You Can? Frank Abagnale, the main character, is a master of social engineering. He convinces people he’s an airline pilot, doctor, and attorney by forging documents and acting like he belongs. The scary thing is, it’s a true story.What’s the problem with social engineering?
© SecurityMetrics | www.securitymetrics.com/pci | 801.705.5665 |
Hey guys and welcome back to the SecurityQ, your source for business data security Today on the SecurityQ, we’re back with part two of social engineering. Alright guys. Last time on the SecurityQ, we talked a little about social engineering and I showed you a pretty sweet example. But today I interviewed two security experts: an auditor and forensics investigator. Here’s what they had to say about social engineering. Social engineering, the part that frustrated us was how easy it was to do this with customers. We’d say, hey we’re here to work on your network or work on your computers, can you show me to your server room? And they’d lead us right back there. They wouldn’t ask us, you should know the password, and I’m gonna give it to you. They’d just give us the password. We would send a letter later on and tell them how easy it was to get inside. They’re always quite surprised. Usually when you go to a company they feel like their people are trained very well. I’ve worked at customer sites where they’ve been really secure and they’ve done a much better job. Bu by far, most companies are lax on their rules and people need better training. There’s another way that it’s kind of unusual. That merchants really need to be on guard for the social engineer. For example, there was a an investigation we were involved in where this guy had very limited IT skills, but he knew how to talk. He simply opened up the yellow pages and started calling all the restaurants in a particular chain that were in this area. He said, I have to do some system maintenance and I can walk you right through it. We’ll do it together over the phone. Enabled a remote session with them, and virtually while he was on the phone with the manager, installed malware. Alright guys, I’ve said it before and I’m gonna say it again. You may have the best technology on the face of the planet, but if you don’t protect yourself from the social threat, you’re leaving your business wide open. Our advice? Train your employees against the social threat and remember to always prepare because your security matters. Well guys that’s all the time we have today on the SecurityQ. But as always, we want to hear from you. So post your questions in the comments below and don’t forget to subscribe. See ya next time on the SecurityQ.wistiaEmbed = Wistia.embed(“5mi8u7k6kc”); Here are some common ways social engineers try to socially engineer us Steal badges and credentials in unlocked carsGo to the local donation store and buy old company T-shirtsPose as janitorial staff to get into a building“Can you hold the door for me? I don’t have my badge.”Pose as an IT person that needs to fix the networkTry unlocked doors around the backside of buildings Pose as law enforcement conducting an inspection Dumpster dive for sensitive documents![]() Here’s what happens when I try to socially engineer someone.
Here’s what happens when I try to socially engineer someone.
© SecurityMetrics | www.securitymetrics.com/pci | 801.705.5665 |
Hey guys, welcome back to the SecurityQ, your source for business data security. Today on the SecurityQ, we’re gonna discuss one topic. The social threat to your business. Here’s the game if you don’t mind if I try. Out of the things you have inside, would you say would be most valuable? The thing inside your pockets We’ll take your front pocket here, do you have something inside? You don’t mind if I bring this out in public do you? I believe that’s really strange. So you have anything else? Okay guys, so we just saw a pretty sweet video of a social engineer, or a con man, stealing personal items from a guy. I have to tell you I’m quite impressed with his skill. Now a lot of businesses ask me, what is a social engineer and how does that apply to my business? The truth is, a social engineer is somebody that uses social interaction to steal data. It could be personal, that data could be physical, that data could be coming from your trash can. It’s data they want. And they’re gonna use any and all tactics to get that data. Now I’m gonna show you what social engineering looks like at an actual business and I’m personally going to do it. Jive Communications, Voice over IP made affordable and reliable, has graciously given us permission to run a simulation. Everyone involved is an actor. Hi how are you? My name is Brandon Barney and I’m the IT director upstairs. I was monitoring our logs this weekend, and it looked like your Wi-Fi was bleeding into ours. If I could jump onto your computer systems real quick and make sure that’s not the case, I’d sure appreciate it. This employee has one have two choices. They’re either going completely fold and give me access to the network, or they’re gonna shut me down. The question is, what are you and your employees going to do? If you’re looking for information or tactics used by these criminals, check out the link for information from PC world. Our advice? Train your employees and test them. There are lots of professionals out there that can assist you in doing this. Remember, your security matters. Well guys, that’s all the time we have for today on the SecurityQ. If you’re looking for detailed information on social engineering, I’m going to be posting a pretty sweet video response. Remember, we want to hear from you so post your questions in the comments below, and don’t forget to subscribe. See you next time on the SecurityQ.wistiaEmbed = Wistia.embed(“deuhcjmzzj”); How to avoid being a victim of social engineeringThe best way to avoid being socially engineered is by educating yourself and your employees. Here are some points you should touch on during training:You should be slightly paranoid (better to be safe than sorry)Social engineers don’t sneak around. They’re confident and friendly. They look like they belong. Don’t be pressured by their convincing ways.Never give out your username/password, badge, PIN, ID number, credit card, or schedule. In essence, never give out sensitive information about you or your company.Ask for a contact to verify why the person needs the information they’re asking forDon’t hold secure doors open for people you don’t knowThe only way to identify if your employees have soaked in all that social engineering knowledge is to test them. You can don a disguise and test them yourself, or enlist the help of a social engineering professional (also called a pen tester), to come onsite and test your employees, experiment with your physical security, and see what interesting information they can find in your trash cans.Have a business security question? Tweet me and you may see your question answered on the next SecurityQ.Brand Barney (CISSP) is an Associate Security Analyst at SecurityMetrics and has over 10 years of compliance, data security, and database management experience. Follow him on Twitter and check out his other blog posts.
Top 10 Types of Phishing Emails
Criminals have countless methods to trick email users.  By: David EllisPhishing is the electronic version of social engineering and has found a huge market in our email-obsessed world. Hackers send fraudulent emails out to tens of thousands of people, hoping a few will click on attached links, documents, or pictures. The goal? Get recipients to willingly provide valuable social security numbers, passwords, banking numbers, PINs, and credit card numbers.
By: David EllisPhishing is the electronic version of social engineering and has found a huge market in our email-obsessed world. Hackers send fraudulent emails out to tens of thousands of people, hoping a few will click on attached links, documents, or pictures. The goal? Get recipients to willingly provide valuable social security numbers, passwords, banking numbers, PINs, and credit card numbers. This is achieved through a few different methods. Sometimes, cybercriminals trick email recipients into opening an email attachment that loads harmful malware onto their system. Other times, they trick recipients into providing sensitive personal information directly via web forms. Either way, these seemingly teeny mistakes could make serious ripples across your organization, compromising either corporate or personal security.SEE ALSO: 7 Ways to Recognize a Phishing Email.Typically, phishers send legitimate-looking emails that appear as though they originated from reputable companies that many people do business with like BestBuy, Amazon, Federal Express, DHL, and PayPal. The emails often ask customers to confirm information or to go to the business site by clicking on a provided link, and often include a statement of impending consequences if you fail to act.Here are a few common ploys cybercriminals use to trick you.1. The Government ManeuverThis type of email looks like it originated from a federal body, such as the FBI, and tries to scare you into providing your information. Common messages include, ‘Your insurance has been denied because of incomplete information. Click here to provide your information.’ Or, ‘Because you illegally downloaded files, your Internet access will be revoked until you enter the requested information in the form below.’
This is achieved through a few different methods. Sometimes, cybercriminals trick email recipients into opening an email attachment that loads harmful malware onto their system. Other times, they trick recipients into providing sensitive personal information directly via web forms. Either way, these seemingly teeny mistakes could make serious ripples across your organization, compromising either corporate or personal security.SEE ALSO: 7 Ways to Recognize a Phishing Email.Typically, phishers send legitimate-looking emails that appear as though they originated from reputable companies that many people do business with like BestBuy, Amazon, Federal Express, DHL, and PayPal. The emails often ask customers to confirm information or to go to the business site by clicking on a provided link, and often include a statement of impending consequences if you fail to act.Here are a few common ploys cybercriminals use to trick you.1. The Government ManeuverThis type of email looks like it originated from a federal body, such as the FBI, and tries to scare you into providing your information. Common messages include, ‘Your insurance has been denied because of incomplete information. Click here to provide your information.’ Or, ‘Because you illegally downloaded files, your Internet access will be revoked until you enter the requested information in the form below.’ 2. The Friend TacticIf an unknown individual claims to know you in an email, you are probably not suffering from amnesia. More than likely, it is an attempt to get you to wire him/her money. A variation on this theme is that one of your known friends is in a foreign country and needs your help. Before you send your ‘friend’ money, give them a call to verify. Your true friend’s email contact list was probably hijacked.
2. The Friend TacticIf an unknown individual claims to know you in an email, you are probably not suffering from amnesia. More than likely, it is an attempt to get you to wire him/her money. A variation on this theme is that one of your known friends is in a foreign country and needs your help. Before you send your ‘friend’ money, give them a call to verify. Your true friend’s email contact list was probably hijacked.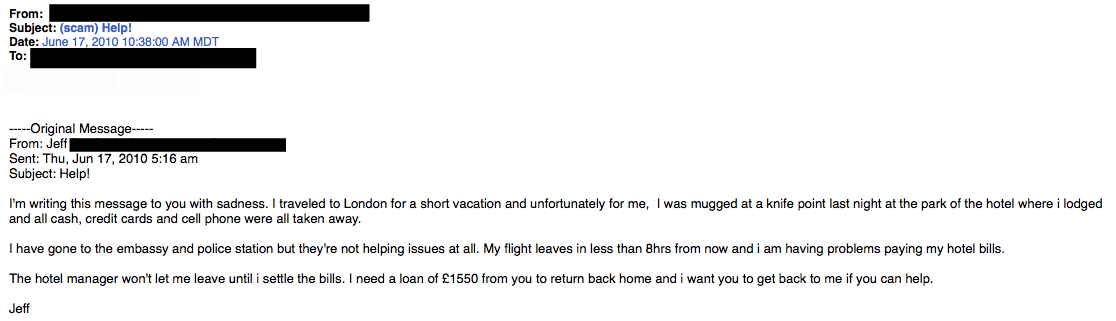 3. The Billing ProblemThis phishing tactic is tricky because it appears quite legitimate. This email states that an item you purchased online cannot be shipped to you because the credit card was expired (or billing address wasn’t correct, etc.). If you click on the provided link, it takes you to a spoofed website and asks for updated payment/shipping information, etc.
3. The Billing ProblemThis phishing tactic is tricky because it appears quite legitimate. This email states that an item you purchased online cannot be shipped to you because the credit card was expired (or billing address wasn’t correct, etc.). If you click on the provided link, it takes you to a spoofed website and asks for updated payment/shipping information, etc.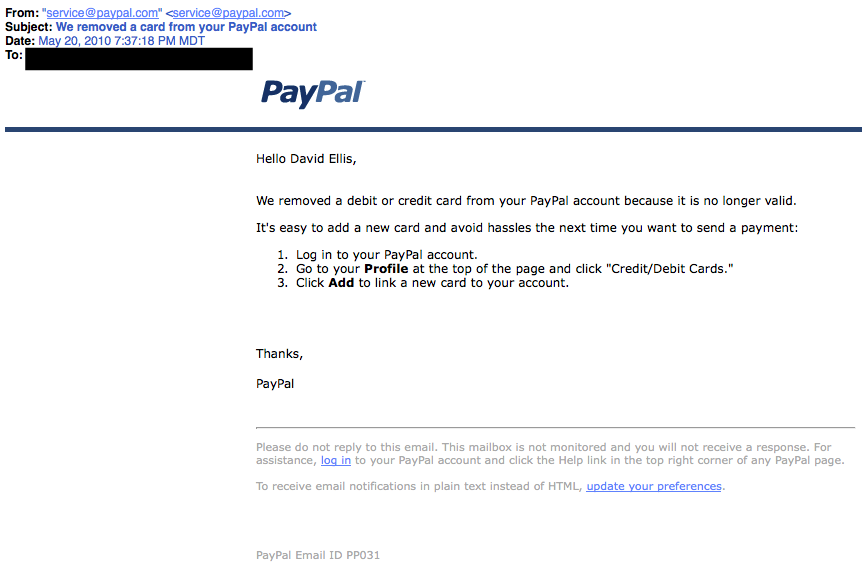 A lot of folks have personal and business PayPal accounts. Here, notice that the email header is from [email protected]. While that may sound legit, everything from PayPal will have an address of …@paypal.com4. The Expiration DateThis type of email falsely explains that your account with [company name] is about to expire, and you must sign in as soon as possible to avoid losing all your data. Conveniently enough, there is a link in the email, which again takes you to a spoofed login page.
A lot of folks have personal and business PayPal accounts. Here, notice that the email header is from [email protected]. While that may sound legit, everything from PayPal will have an address of …@paypal.com4. The Expiration DateThis type of email falsely explains that your account with [company name] is about to expire, and you must sign in as soon as possible to avoid losing all your data. Conveniently enough, there is a link in the email, which again takes you to a spoofed login page. 5. The Virus ScareThis type of email states that your computer has been infected! In order to avoid losing your data and infecting your computer the email instructs you to follow the provided link, or download the “anti-virus” attachment.
5. The Virus ScareThis type of email states that your computer has been infected! In order to avoid losing your data and infecting your computer the email instructs you to follow the provided link, or download the “anti-virus” attachment.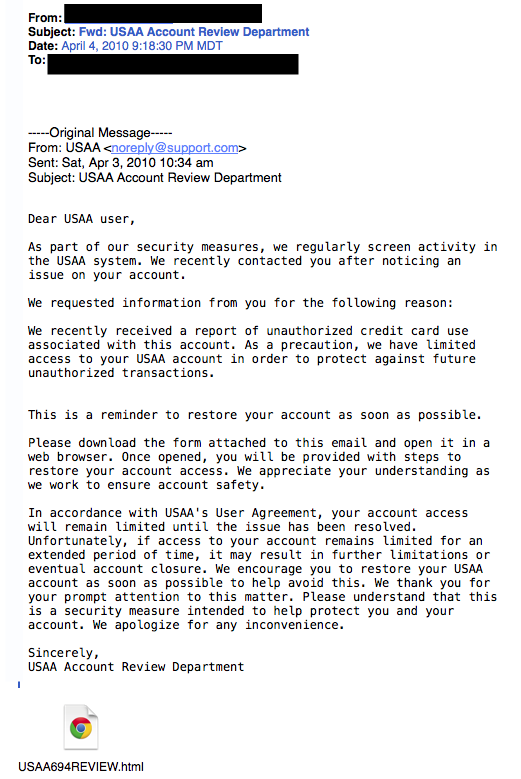 Whatever you do, DON’T CLICK ON THE LINK!6. The Contest WinnerDon’t get too excited when you receive emails that claim you’ve won something, or received an inheritance from a relative you’ve never heard of. 99.9% of the time, these are absolutely bogus. To claim your prize, the email requires you click a link and enter your info for prize shipment.
Whatever you do, DON’T CLICK ON THE LINK!6. The Contest WinnerDon’t get too excited when you receive emails that claim you’ve won something, or received an inheritance from a relative you’ve never heard of. 99.9% of the time, these are absolutely bogus. To claim your prize, the email requires you click a link and enter your info for prize shipment. 7. The Friendly BankYour bank may offer account notifications when certain amounts are withdrawn from your accounts. This ploy tricks you with a fake account notification stating that an amount has been withdrawn from your account that exceeds your notification limit. If you have any questions about this withdrawal (which you probably would), it gives you a convenient link that leads to a web form asking for your bank account number “for verification purposes.” Instead of clicking on the link, give your bank a call. They may want to take action on the malicious email.
7. The Friendly BankYour bank may offer account notifications when certain amounts are withdrawn from your accounts. This ploy tricks you with a fake account notification stating that an amount has been withdrawn from your account that exceeds your notification limit. If you have any questions about this withdrawal (which you probably would), it gives you a convenient link that leads to a web form asking for your bank account number “for verification purposes.” Instead of clicking on the link, give your bank a call. They may want to take action on the malicious email.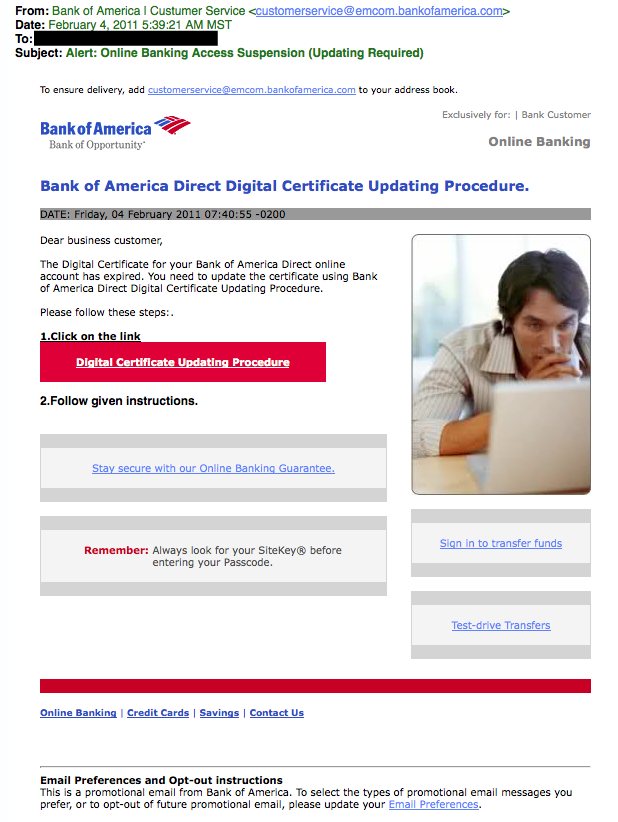 Due to the graphics and opt-out instructions, this phishing attempt seems very legitimate.8. The VictimBeing wrongly accused of something doesn’t feel good. This type of phishing email acts as an angry customer whom supposedly sent you money in return for a shipped product. The email concludes with the threat that they will inform the authorities if they don’t hear from you.
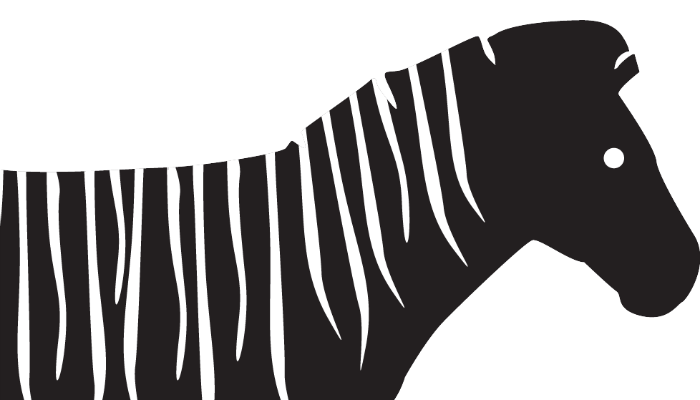
Due to the graphics and opt-out instructions, this phishing attempt seems very legitimate.8. The VictimBeing wrongly accused of something doesn’t feel good. This type of phishing email acts as an angry customer whom supposedly sent you money in return for a shipped product. The email concludes with the threat that they will inform the authorities if they don’t hear from you. This is another type of victim scam. Who wouldn’t be a little worried after receiving this email?9. The Tax CommunicationPractically everyone has annual taxes to submit. That’s why this phishing attempt is so popular. The message states that you are either eligible to receive a tax refund, or you have been selected to be audited. It then requests that you submit a tax refund request or tax form.
This is another type of victim scam. Who wouldn’t be a little worried after receiving this email?9. The Tax CommunicationPractically everyone has annual taxes to submit. That’s why this phishing attempt is so popular. The message states that you are either eligible to receive a tax refund, or you have been selected to be audited. It then requests that you submit a tax refund request or tax form. 10. The CheckupThis is one of the more unassuming phishing email attempts. It claims [company name] is conducting a routine security procedure and requests you verify your account by providing information. This scam is especially effective if you happen to be a customer of the named business.
10. The CheckupThis is one of the more unassuming phishing email attempts. It claims [company name] is conducting a routine security procedure and requests you verify your account by providing information. This scam is especially effective if you happen to be a customer of the named business. If you receive a phishing email:Don’t click on any links, open attachments, or expand any included picturesDon’t try to reply to the senderReport the scam (forward the e-mail to the FTC – [email protected])Delete the email from your computerIf you do legitimate business with a company mentioned in the phishing email, you can call the business and ask if they would like you to forward the email to them, so they may take further action.Was this post helpful? Share it!David Ellis (GCIH, QSA, PFI, CISSP) is Director of Forensic Investigations at SecurityMetrics with over 25 years of law enforcement and investigative experience. Check out his other blog posts.
If you receive a phishing email:Don’t click on any links, open attachments, or expand any included picturesDon’t try to reply to the senderReport the scam (forward the e-mail to the FTC – [email protected])Delete the email from your computerIf you do legitimate business with a company mentioned in the phishing email, you can call the business and ask if they would like you to forward the email to them, so they may take further action.Was this post helpful? Share it!David Ellis (GCIH, QSA, PFI, CISSP) is Director of Forensic Investigations at SecurityMetrics with over 25 years of law enforcement and investigative experience. Check out his other blog posts.
- « Previous Page
- 1
- 2
- 3
- 4
- 5
- …
- 16
- Next Page »
 What businesses can learn from armadillos, seahorses, and zebras.
What businesses can learn from armadillos, seahorses, and zebras.  After all, gullible employees lead to security breaches.
After all, gullible employees lead to security breaches.  Criminals have countless methods to trick email users.
Criminals have countless methods to trick email users.