 Soooo…. You’ve been on Facebook a while and you’ve set your privacy settings to whatever new super-secret stealthy hidden mode setting Facebook has. You probably also feel like none of your 400+ friends would ever tell anyone what you post. You look at articles about people posting things they shouldn’t going viral and you think “I’m so glad that’s not me. I would never do something like that.” I destroy that myth everyday at my job. In real life, I investigate leads in criminal cases which can aid my clients. A favorite place I go for these leads is social media.When I tell people I go to Facebook for leads, the first thing they like to say is “Well, you’re not going to find anything on me like that.” I’m polite so I smile and tell them “Probably not.” Of course, I’m lying. If I’ve told you that, this is where you’re probably feeling a little uneasy. Let’s be clear, if I don’t have an interest in finding something, I probably won’t find it. That’s not to say I can’t because I assure you I can.So, let’s breakdown how I might do a social media query. I won’t bore you with site specifics but I will address some things that are common throughout the social media investigations landscape. This is not to scare you. I am merely trying to inform you so you understand exactly what information you voluntarily give away.Disclaimer: For the experts: This in not all-inclusive and I’m aware of the many advances in social media investigations. This is mainly informative for those who may not know and to spark some discussion. All others: Please check whatever jurisdiction for whatever legalities may exist for you.The best way to illustrate this topic is to assume you’ll be doing a search yourself. If you don’t mind being spooked, try this on yourself assuming you’re a complete stranger who’s only been given the task of obtaining whatever information exists on you in social media. I recommend creating your own “blank” account that you have no affiliation with to get started. When we get to associates, feel free to pretend and assume the worse about people on your friends list you haven’t seen or spoken to in some time. Start with a subject. Having a name (preferably a first and last name is good). I’ve done this with neither. More on that later.Put the name in the search box of the social media site you’re searching. This fruitful if you’re seeing if someone is on the site or if the profile is possibly “hidden” from searches. The latter requires for you to know the subject is actually on the site. While doing this, play around with nicknames or aliases. A personal favorite of mine are email addresses. I also use their most used username if I know it. I have also looked up last names only just to see if someone posts things to a relative’s profile.When searching Google, try to place quotations marks at the beginning and end of your subject’s name. Also, type in site:whatever-the-social-media-site-you-think-they-are-on.com/net/org/edu/gov. Novice searchers give up because the results are too many. This narrows it down quite a bit.Despite what you think, no name is too common for a determined investigator. There are other things than our names that differentiate us. For example, your name is “John Smith”. That’s too common of a name for some investigators. But what happens when I search for “John Smith” in Dayton, OH who is a police officer married to a woman named Ebony? If you’re the target, you’re not as anonymous as you thought.Search them by username and old phone numbers. Sometimes, this is all you have to go on. Do it. That username may be their most commonly used one for everything. This could lead to old social media profiles (a time machine treasure trove of forgotten pics, lifetime issues and events, contacts, etc.), photo-sharing sites they frequent, articles they bookmark (Pinterest), comments they’ve made on other sites (Youtube can be great for this stuff), and sites they don’t want anyone to know they frequent. Getting the username can be tricky. If I have a confirmed profile for them, I’ll take the username that is in the profile’s URL and then perform an “exact phrase” search on Google.I like to try the phone numbers search quite a bit. I’m not looking for an address neccessarily if it’s a social media investigation. Some profiles are only searchable with a phone number. Also people post their numbers on sites that don’t value privacy. For example, you run a shop that sells auto parts. As such, you belonged to a parts forum online. There you posted your number to get orders under a username I never knew existed. Not only do I have historical data on you possibly but I may also get a look at your posts there as well whatever I can dig up on this old username.If none of this proves fruitful, try a Google Image search. You may not be aware of this but Google now allows you to search by image. That means, I don’t need your name to find you on the Internet. Sometimes, I find people use the same photo for most sites they frequent. Perhaps, you’ll find a site with a picture you have and can dig up useful information such as other pictures, other usernames, and most importantly, associates.Associates are where the money is. Seriously, most people assume, wrongly, their Facebook friends feel the same way they do about things or they feel some impunity with what they post to their audience. In some cases, this may be true. However, I can guarantee it probably is not. Finding associates can be tricky if you don’t know much about your subject. Hopefully, Google will help you out here. If not, I recommend spending the $19.95 to use people-search sites like Intelius or Spokeo. This should give you a list of names of people who either know your subject or lived in the same area as him. Also, try Classmates.com. Someone went to high school with your subject and I bet you they’re still on their Facebook friend’s list. Another feature of some site’s search engines is the suggest friend’s list. If you’re friends with their friends, social media sites like to let you know and ask if you want to be your subject’s friend. Of course, you don’t. But this provides with that profile you’ve been looking for or at least one of them.Old friendships are tricky. We think the people who have known us the longest have our best interests at heart. Let me assure, some of them don’t. Most people trust these folks with lots of personal information, when they go on a tirade or a rant. The simple truth is if someone has it in for you, they can voluntarily give anyone access to whatever you share with them online.
Soooo…. You’ve been on Facebook a while and you’ve set your privacy settings to whatever new super-secret stealthy hidden mode setting Facebook has. You probably also feel like none of your 400+ friends would ever tell anyone what you post. You look at articles about people posting things they shouldn’t going viral and you think “I’m so glad that’s not me. I would never do something like that.” I destroy that myth everyday at my job. In real life, I investigate leads in criminal cases which can aid my clients. A favorite place I go for these leads is social media.When I tell people I go to Facebook for leads, the first thing they like to say is “Well, you’re not going to find anything on me like that.” I’m polite so I smile and tell them “Probably not.” Of course, I’m lying. If I’ve told you that, this is where you’re probably feeling a little uneasy. Let’s be clear, if I don’t have an interest in finding something, I probably won’t find it. That’s not to say I can’t because I assure you I can.So, let’s breakdown how I might do a social media query. I won’t bore you with site specifics but I will address some things that are common throughout the social media investigations landscape. This is not to scare you. I am merely trying to inform you so you understand exactly what information you voluntarily give away.Disclaimer: For the experts: This in not all-inclusive and I’m aware of the many advances in social media investigations. This is mainly informative for those who may not know and to spark some discussion. All others: Please check whatever jurisdiction for whatever legalities may exist for you.The best way to illustrate this topic is to assume you’ll be doing a search yourself. If you don’t mind being spooked, try this on yourself assuming you’re a complete stranger who’s only been given the task of obtaining whatever information exists on you in social media. I recommend creating your own “blank” account that you have no affiliation with to get started. When we get to associates, feel free to pretend and assume the worse about people on your friends list you haven’t seen or spoken to in some time. Start with a subject. Having a name (preferably a first and last name is good). I’ve done this with neither. More on that later.Put the name in the search box of the social media site you’re searching. This fruitful if you’re seeing if someone is on the site or if the profile is possibly “hidden” from searches. The latter requires for you to know the subject is actually on the site. While doing this, play around with nicknames or aliases. A personal favorite of mine are email addresses. I also use their most used username if I know it. I have also looked up last names only just to see if someone posts things to a relative’s profile.When searching Google, try to place quotations marks at the beginning and end of your subject’s name. Also, type in site:whatever-the-social-media-site-you-think-they-are-on.com/net/org/edu/gov. Novice searchers give up because the results are too many. This narrows it down quite a bit.Despite what you think, no name is too common for a determined investigator. There are other things than our names that differentiate us. For example, your name is “John Smith”. That’s too common of a name for some investigators. But what happens when I search for “John Smith” in Dayton, OH who is a police officer married to a woman named Ebony? If you’re the target, you’re not as anonymous as you thought.Search them by username and old phone numbers. Sometimes, this is all you have to go on. Do it. That username may be their most commonly used one for everything. This could lead to old social media profiles (a time machine treasure trove of forgotten pics, lifetime issues and events, contacts, etc.), photo-sharing sites they frequent, articles they bookmark (Pinterest), comments they’ve made on other sites (Youtube can be great for this stuff), and sites they don’t want anyone to know they frequent. Getting the username can be tricky. If I have a confirmed profile for them, I’ll take the username that is in the profile’s URL and then perform an “exact phrase” search on Google.I like to try the phone numbers search quite a bit. I’m not looking for an address neccessarily if it’s a social media investigation. Some profiles are only searchable with a phone number. Also people post their numbers on sites that don’t value privacy. For example, you run a shop that sells auto parts. As such, you belonged to a parts forum online. There you posted your number to get orders under a username I never knew existed. Not only do I have historical data on you possibly but I may also get a look at your posts there as well whatever I can dig up on this old username.If none of this proves fruitful, try a Google Image search. You may not be aware of this but Google now allows you to search by image. That means, I don’t need your name to find you on the Internet. Sometimes, I find people use the same photo for most sites they frequent. Perhaps, you’ll find a site with a picture you have and can dig up useful information such as other pictures, other usernames, and most importantly, associates.Associates are where the money is. Seriously, most people assume, wrongly, their Facebook friends feel the same way they do about things or they feel some impunity with what they post to their audience. In some cases, this may be true. However, I can guarantee it probably is not. Finding associates can be tricky if you don’t know much about your subject. Hopefully, Google will help you out here. If not, I recommend spending the $19.95 to use people-search sites like Intelius or Spokeo. This should give you a list of names of people who either know your subject or lived in the same area as him. Also, try Classmates.com. Someone went to high school with your subject and I bet you they’re still on their Facebook friend’s list. Another feature of some site’s search engines is the suggest friend’s list. If you’re friends with their friends, social media sites like to let you know and ask if you want to be your subject’s friend. Of course, you don’t. But this provides with that profile you’ve been looking for or at least one of them.Old friendships are tricky. We think the people who have known us the longest have our best interests at heart. Let me assure, some of them don’t. Most people trust these folks with lots of personal information, when they go on a tirade or a rant. The simple truth is if someone has it in for you, they can voluntarily give anyone access to whatever you share with them online. This young lady thought she was being “funny” outside of Arlington. Several of her “friends” didn’t think so. Be careful what you “like”. People wrongly assume the pages they like or the comments they reply to on someone else’s page is somehow protected. Yeah, that is totally wrong. It is protected ONLY if they have set themselves up with the strictest privacy settings. Many times, a person’s “likes” can reveal about themselves even if an investigator can’t see anything else. A great example are Facebook Groups which advocate violence or are sexually explicit. Unfortunately, people forget to hide what pages they “like” and it suddenly has some bearing on something they never imagined it would.Search for a name in a foreign language. I see you laughing but I once had someone hide their profile by using another language to hide their name. It’s a great idea but as I ran out of options, I went to Google Translate and entered the subject’s name from English to Korean. Suddenly, her profile appeared.Search their friends’ friends list. Some people hide in plain sight. You may be searching for the right subject but entered the wrong letter. A friend’s friends list will probably have the name as something else.Search EVERY PHOTO, LOCATION TAG, EVENT SIGN-IN, etc. Sometimes, the information we seek is in places we dismiss as being “dry”. Look through EVERYTHING. Trust me. This alone can give you more associates, state of mind of your subject, places they’ve been or frequent, events they’ve been or locations they can be expected to be at, and all the drama that comes with social media picture posting.When you’ve found what you’re looking for, archive it. This sounds easier than you think. Grab your smartphone and take a picture of your screen where the information is. People trust screenshots more than they do a link they can click.Do this exercise on yourself and assume your current or future employer, spouse, child custody judge, friends, family, and others are doing the same. Those who get their 15 minutes of fame from poor Facebook posts never seem to think they’d get turned in by their “friends”. Also, here’s a tidbit – if you’re posting information you shouldn’t, never exclaim “I don’t care who sees this.” I GUARANTEE you will.*Some places I like to go to search for social media investigation querieswww.spokeo.comwww.pipl.comwww.linkedin.comwww.facebook.comwww.twitter.comwww.google.comimages.google.comwww.whitepages.comwww.intelius.comwww.blackbookonline.infowww.topsy.com *You’re not getting all of my trade secrets
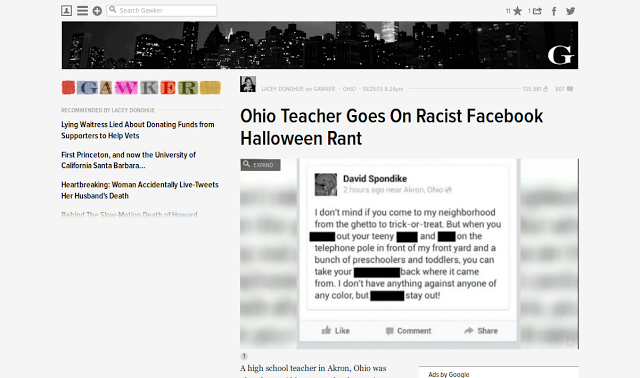
This young lady thought she was being “funny” outside of Arlington. Several of her “friends” didn’t think so. Be careful what you “like”. People wrongly assume the pages they like or the comments they reply to on someone else’s page is somehow protected. Yeah, that is totally wrong. It is protected ONLY if they have set themselves up with the strictest privacy settings. Many times, a person’s “likes” can reveal about themselves even if an investigator can’t see anything else. A great example are Facebook Groups which advocate violence or are sexually explicit. Unfortunately, people forget to hide what pages they “like” and it suddenly has some bearing on something they never imagined it would.Search for a name in a foreign language. I see you laughing but I once had someone hide their profile by using another language to hide their name. It’s a great idea but as I ran out of options, I went to Google Translate and entered the subject’s name from English to Korean. Suddenly, her profile appeared.Search their friends’ friends list. Some people hide in plain sight. You may be searching for the right subject but entered the wrong letter. A friend’s friends list will probably have the name as something else.Search EVERY PHOTO, LOCATION TAG, EVENT SIGN-IN, etc. Sometimes, the information we seek is in places we dismiss as being “dry”. Look through EVERYTHING. Trust me. This alone can give you more associates, state of mind of your subject, places they’ve been or frequent, events they’ve been or locations they can be expected to be at, and all the drama that comes with social media picture posting.When you’ve found what you’re looking for, archive it. This sounds easier than you think. Grab your smartphone and take a picture of your screen where the information is. People trust screenshots more than they do a link they can click.Do this exercise on yourself and assume your current or future employer, spouse, child custody judge, friends, family, and others are doing the same. Those who get their 15 minutes of fame from poor Facebook posts never seem to think they’d get turned in by their “friends”. Also, here’s a tidbit – if you’re posting information you shouldn’t, never exclaim “I don’t care who sees this.” I GUARANTEE you will.*Some places I like to go to search for social media investigation querieswww.spokeo.comwww.pipl.comwww.linkedin.comwww.facebook.comwww.twitter.comwww.google.comimages.google.comwww.whitepages.comwww.intelius.comwww.blackbookonline.infowww.topsy.com *You’re not getting all of my trade secrets
The Rules: 10 Things Every Entry-level Security Person Needs to Know & Every Pro Forgets
 There are principles which are inherently the same no matter what discipline of security you practice. Although, for some reason, some of us tend to forget them to our detriment. I blame 99.9% of all practitioner -caused security failures on this. What’s worse is that rookies aren’t the only one’s who miss them. A lot of these issues come from pros who should know better. Like everything else, we need a refresher.
There are principles which are inherently the same no matter what discipline of security you practice. Although, for some reason, some of us tend to forget them to our detriment. I blame 99.9% of all practitioner -caused security failures on this. What’s worse is that rookies aren’t the only one’s who miss them. A lot of these issues come from pros who should know better. Like everything else, we need a refresher.
Our business is about risk. This profession isn’t just about assigning widgets to fix people’s security issues. We deal with asking and solving really tough questions the end-user is often scared to address or doesn’t know exist. If you’re just selling a product to meet a quota or performing a security function to satisfy a job description, you’re wrong. Start by asking the client about the resources he’s protecting and what he’s willing to do to protect it. Next, ask him if it’s worth protecting. Most people believe EVERYTHING needs security. Precious time and resources are sometimes wasted defending something no one cares about to include the bad guys.Security is a state of mind; not an objective. Do you know how many of us believe the mythology that tells us we can attain security as if it were quantitative? Of course you do. An entire industry is built around this ridiculous premise. Nothing is 100% secure – ever! It can’t be. There’s always a vulnerability. I’m not saying not to bother with security. I’m just asking you to consider what it is you’re trying to do and to consider if you and the client have realistic goals.Know your tools. I’m surprised by the number of practitioners who know so little about the tools that are available to protect their assets. People have this problematic tendency to learn from vendors about the tools offered but fail to educate themselves. Venture to some trade shows. Join ASIS. Ask around the Internet. Become a sponge. Too many of us are bricks. There aren’t enough of us taking in knowledge in order to give knowledge back.Know your limitations. Face it, there are some problems you can’t fix. Seriously. If you can’t do the job, be honest. Say you can’t and find someone else who can. You’ll keep your integrity and impress the client more by being honest. You’ll also develop a good rapport with trusted colleagues you refer. Trust me this is a good thing. After the referral, tag along. Be that sponge I mentioned previously.Define your goals. When I was a supervisor in the Air Force, I can’t tell you how many of my troops’ professional failings came from forgeting this simple step. Look, no one likes writing goals except for those insanely productive people who live inside Lifehacker. But what’s the harm in sitting down and mapping out your weaknesses, what you can to do to fix them, and assigning a goal to reach them? Absolutely nothing. So get started.
This can and should also be applied to security projects. Define what the project is, what the client’s expectations are, determine how you can meet them, and then set goals in order to meet each objective. It’s simple but few people do it. Failing to do it guarantees you’ll lose an opportunity to work on future projects. Know your terrain. Do you really understand the security environment? I’m not just talking about the threat. So often, we ignore the internal and external impacts of our measures which undermine our ability to properly protect these assets. For example, in many businesses, there is a key exchange. If you need access to a secure area, you have to leave a badge to receive a key into the area. This seems like a perfectly harmless idea, until users grow tired of giving up their badges and the person conducting the exchange is increasingly wary of having to do it. Security lapses occur as the “inconvenience” outweighs the security concerns. Don’t believe me? Three words – Transportation Security Administration. Learn the terrain and figure out what will work the smoothest.Education begins with exposure. My take on security education is simple – you don’t know what you need to know because you’re not out there asking the right people. I know some people may be scratching their heads at that. But it’s the truth. So many of us are ignorant of the threat, the tools, and the terrain because we haven’t taken the steps to “get smart” about them.Befriend your enemy. I’m not telling you to “friend request” al-Shabab on Facebook or chat with MS-13 members on Twitter. What I’m suggesting is that you not only read up on their operations but try to get some basic understanding of their collective psychology. Learn how they conduct target selection, who they work with, how they recruit, their tools, etc. This will not only give you an idea as to how to build a better security plan but it will also enable you to ensure it’s both comprehensive and adaptive.Everyone has a sales pitch. My first venture into private security was interesting, to say the least. I learned a lot from that gig. One of the lessons that stood out the most was to always be on the lookout for the sale pitch. Learning your client’s pitch will enable you to ensure how you protect his resources won’t effect his “bottom-line”. Would be it a good idea to have dome cameras installed over tables at restaurants? Of course not. What most restaurants sell, in addition to food, is a friendly environment where you can dine among friends. A dome camera over your table robs you of that, thus killing the restaurant’s sale pitch. I’ve never seen that happen but it does illustrate how quickly we can lose the client’s respect and business by forgetting they have a business to run as well. Vigilance is demanded. When I wrote the first draft of this article, I originally wrote “vigilance is expected.” That was a HUGE mistake. Why? Because “expected” means you accept a margin of failure. In this business, apathy is where all good security measures go to die. I recognize the fine line between hyper-vigilance and vigilance. Certainly, there needs to be a balance. Just remember, at the end of the day, when there is a breach, you’ll be forced to address why you violated this most sacred of security “rules”. If you’re a supervisor, your vision of how your people practice their profession should have this rule at the forefront. Julius Ceasar had a special patrol he conducted before battle to catch wayward soldiers sleep on their post. The maximum and usual penalty? Death. While the consequences aren’t quite as dire as this in the real world at times, complacency will destroy our ability to adequately protect the client and their resources. This is a compromise we can’t afford to allow – EVER.
Ten OPSEC Lessons Learned From The Good Guys, Bad Guys, and People-in-Between
If you’ve been in the security world long enough, you’ve heard of a term called “OPSEC” or operational security. This is a security discipline in which organizations or individual operators conduct their business in a manner that does not jeopardize their true mission. If you’re a police officer who is staking out a house, it would be bad OPSEC to sit outside the house in a marked police vehicle. I think it’s prudent we discuss this discipline so we can better analyze our own processes by which we protect ourselves and our operations. Reviewing the OPSEC process is a great place to start. The following come from Wikipedia (I know – it’s super-scholarly):
Identification of Critical Information: Identifying information needed by an adversary, which focuses the remainder of the OPSEC process on protecting vital information, rather than attempting to protect all classified or sensitive unclassified information.Analysis of Threats: the research and analysis of intelligence, counterintelligence, and open source information to identify likely adversaries to a planned operation.Analysis of Vulnerabilities: examining each aspect of the planned operation to identify OPSEC indicators that could reveal critical information and then comparing those indicators with the adversary’s intelligence collection capabilities identified in the previous action.Assessment of Risk: First, planners analyze the vulnerabilities identified in the previous action and identify possible OPSEC measures for each vulnerability. Second, specific OPSEC measures are selected for execution based upon a risk assessment done by the commander and staff.Application of Appropriate OPSEC Measures: The command implements the OPSEC measures selected in the assessment of risk action or, in the case of planned future operations and activities, includes the measures in specific OPSEC plans.Assessment of Insider Knowledge: Assessing and ensuring employees, contractors, and key personnel having access to critical or sensitive information practice and maintain proper OPSEC measures by organizational security elements; whether by open assessment or covert assessment in order to evaluate the information being processed and/or handled on all levels of operatability (employees/mid-level/senior management) and prevent unintended/intentional disclosure.We should also recognize good guys aren’t the only ones who practice this discipline. As a matter of fact, the bad guys do as well and many are quite good at it. The lessons we could learn from them, our fellow security professionals, and others are almost immeasurable.
NEVER trust a big butt and a smile. Yup. I started off with that. Bear with me. Many intelligence agencies and law enforcement organizations use sex as a means to get close to a target or person of interest. Most bad guys realize this. However, many do not to their own detriment. When involved with people in a relationship or sexual encounter, they get very close to you and your secrets. I liken these people to “trusted agents” who you allow close enough to you that can get more information than you’re willing or able to share publicly. Poor OPSEC practitioners often forget this. Most of their security failures stem from this fatal flaw. I’m not saying to not be in a relationship or to eschew intimacy. If you’re in a job that requires you adhere to sound OPSEC principles, what I’m advising you to do is to exercise due diligence and conduct a risk analysis before you do. Think Marion Barry, Anthony Weiner, and Elliott Spitzer. Immortal words spoken during an EPIC fail.Always have a thoroughly vetted back-story for your cover. This is commonly referred to as “legend” in the intelligence community. This is an identity in line with your established, synthetic cover. For example, I previously mentioned the hacker known as the The Jester in a previous blog post. Depending on which side you’re on, he’s either a bad guy or a good guy. However, the lessons he teaches us about cover are insightful. Whenever someone “doxes” him, he has a prepared and detailed analysis as to how he created that cover identity. Many times he’ll use a name that does exist with a person who either does not exist or who he has cleverly manufactured using a multitude of identity generators. He’ll use disposable credit cards, email, LinkedIn profiles, VPNs which show logins from his cover location, etc. He even engages in cyber-deception with other actors to establish various cover stories for operations that require them. Whether you like him or not, he’s certainly good at one thing we know for sure – cover discipline.NEVER trust anyone you just met. I see you laughing. Many people mistakenly believe they can and should trust everyone they meet. They will often claim they don’t but their behavior says otherwise. As Ronald Reagan is often quoted is saying, “In God we trust, all others we verify” I firmly believe this to be the most crucial aspect of operational security. Proper trust is needed in any environment for the mission to be accomplished. However, blind trust can and will kill any hopes of a successful mission. Whether you’re checking identification at an entry control point or planning cybersecurity for an online bank, you should always treat every introduction you don’t initiate as suspect. Then triage people and their level of access according to risk acceptance. This is a lesson we learned with Edward Snowden. He’d only been at Booze Hamilton a few months before he began siphoning massive amounts of classified information he had no direct access or need-to-know. Another saying I’m fond of is “Keep your enemies close, but your friends closer.” I’m not saying everyone you meet is going to steal from you or betray your trust. Like my momma always says, “Not everyone that smiles at you is your friend and not every frown comes from an enemy.”Shut the hell up! No. Seriously. Shut up. If you hang around the special operations community, you’ll hear a term used to describe the work they do as “quiet professionals”. Most successful bad guys realize the best way to ensure longevity to shut the hell up. Bragging about or giving “pre-game commentary” before an operation are guaranteed ways to get caught or killed. The truly dangerous people are the one’s who never say a word and just do their work. Sometimes, lethality is best expressed with silence.
Immortal words spoken during an EPIC fail.Always have a thoroughly vetted back-story for your cover. This is commonly referred to as “legend” in the intelligence community. This is an identity in line with your established, synthetic cover. For example, I previously mentioned the hacker known as the The Jester in a previous blog post. Depending on which side you’re on, he’s either a bad guy or a good guy. However, the lessons he teaches us about cover are insightful. Whenever someone “doxes” him, he has a prepared and detailed analysis as to how he created that cover identity. Many times he’ll use a name that does exist with a person who either does not exist or who he has cleverly manufactured using a multitude of identity generators. He’ll use disposable credit cards, email, LinkedIn profiles, VPNs which show logins from his cover location, etc. He even engages in cyber-deception with other actors to establish various cover stories for operations that require them. Whether you like him or not, he’s certainly good at one thing we know for sure – cover discipline.NEVER trust anyone you just met. I see you laughing. Many people mistakenly believe they can and should trust everyone they meet. They will often claim they don’t but their behavior says otherwise. As Ronald Reagan is often quoted is saying, “In God we trust, all others we verify” I firmly believe this to be the most crucial aspect of operational security. Proper trust is needed in any environment for the mission to be accomplished. However, blind trust can and will kill any hopes of a successful mission. Whether you’re checking identification at an entry control point or planning cybersecurity for an online bank, you should always treat every introduction you don’t initiate as suspect. Then triage people and their level of access according to risk acceptance. This is a lesson we learned with Edward Snowden. He’d only been at Booze Hamilton a few months before he began siphoning massive amounts of classified information he had no direct access or need-to-know. Another saying I’m fond of is “Keep your enemies close, but your friends closer.” I’m not saying everyone you meet is going to steal from you or betray your trust. Like my momma always says, “Not everyone that smiles at you is your friend and not every frown comes from an enemy.”Shut the hell up! No. Seriously. Shut up. If you hang around the special operations community, you’ll hear a term used to describe the work they do as “quiet professionals”. Most successful bad guys realize the best way to ensure longevity to shut the hell up. Bragging about or giving “pre-game commentary” before an operation are guaranteed ways to get caught or killed. The truly dangerous people are the one’s who never say a word and just do their work. Sometimes, lethality is best expressed with silence.

Watch what you leak. While we can keep our mouths shut, it is more difficult in the information age to keep everything connected to us quiet. In order to properly protect ourselves, we have to begin this process by conducting proper risk analysis. Is what I’m doing right now giving away something I don’t want the public to know? Is the the device or medium I’m talking on able to give away information I’m not comfortable with sharing? Does my enemy have the ability to intercept or analyze what I’m doing in order to gain sensitive information? What “tells” am I projecting? These are a few of many questions you should be asking in order to ensure you’re limiting “noise litter”.
 In the information age, do I need to say more?If you’re doing secret stuff, NEVER EVER EVER EVER EVER, talk on the wire. Look at the Mafia as a perfect example of what not to do. As an OPSEC practitioner, you should never communicate on any medium that can give away your secrets or be intercepted. John Gotti got busted talking on the wire. A person rule of thumb: If it can receive messages, it can transmit messages without you knowing. Treat every computer like an informant – feed it what you’re willing to share with your adversary.NEVER ever touch or be in the same place as the “product”. For the uninitiated, that is one of first rules of the dope game. Every successfully, elusive drug dealer knows to keep away from the “product” (read “drugs). Whatever the “product” in your “game”, ensure you put enough distance between you and it. If you have to be close to it, then have a good reason to be with it.Recognize “the lion in the tall grass”. When practicing OPSEC, if there is one thing you should never forget is why you’re doing it. The reason you’re practicing it is simple – there are people out there that oppose you. Ignore them at your detriment.NEVER say something you can’t backup or prove immediately. Nothing says you’re a person needing to be checked out better than saying things you can backup or prove. People who are trying to vet you will require you backup what you say for a reason. Be ready for this. A great example of this is demonstrated by people who claim to be connected to someone of stature in order to gain access. In this case, they’re found out because the target asked the other party who could not confirm this.Treat your real intentions and identity as that gold ring from Lord of the Rings. I’m not saying put your driver’s license on a necklace so a troll who think it’s his “precious” won’t take it. First of all, that’s too cool to happen in real life. Second, you’ll look like an idiot. Finally, there are more practical ways of protecting your identity. For starters, never have anything that connects your identity to your operation. Next, if you have to use your real identity in connection with an operation, give yourself some ability to deny the connection. Lastly, NEVER trust your identity, intentions, or operations to anyone or anything other than yourself.I’ve decided to include the more practical list from the “Notorious B.I.G.” to drive home some of these principles:
In the information age, do I need to say more?If you’re doing secret stuff, NEVER EVER EVER EVER EVER, talk on the wire. Look at the Mafia as a perfect example of what not to do. As an OPSEC practitioner, you should never communicate on any medium that can give away your secrets or be intercepted. John Gotti got busted talking on the wire. A person rule of thumb: If it can receive messages, it can transmit messages without you knowing. Treat every computer like an informant – feed it what you’re willing to share with your adversary.NEVER ever touch or be in the same place as the “product”. For the uninitiated, that is one of first rules of the dope game. Every successfully, elusive drug dealer knows to keep away from the “product” (read “drugs). Whatever the “product” in your “game”, ensure you put enough distance between you and it. If you have to be close to it, then have a good reason to be with it.Recognize “the lion in the tall grass”. When practicing OPSEC, if there is one thing you should never forget is why you’re doing it. The reason you’re practicing it is simple – there are people out there that oppose you. Ignore them at your detriment.NEVER say something you can’t backup or prove immediately. Nothing says you’re a person needing to be checked out better than saying things you can backup or prove. People who are trying to vet you will require you backup what you say for a reason. Be ready for this. A great example of this is demonstrated by people who claim to be connected to someone of stature in order to gain access. In this case, they’re found out because the target asked the other party who could not confirm this.Treat your real intentions and identity as that gold ring from Lord of the Rings. I’m not saying put your driver’s license on a necklace so a troll who think it’s his “precious” won’t take it. First of all, that’s too cool to happen in real life. Second, you’ll look like an idiot. Finally, there are more practical ways of protecting your identity. For starters, never have anything that connects your identity to your operation. Next, if you have to use your real identity in connection with an operation, give yourself some ability to deny the connection. Lastly, NEVER trust your identity, intentions, or operations to anyone or anything other than yourself.I’ve decided to include the more practical list from the “Notorious B.I.G.” to drive home some of these principles:
TEN CRACK COMMANDMENTSRule number uno, never let no one know
How much, dough you hold, ’cause you know
The cheddar breed jealousy ‘specially
If that man *** up, get your *** stuck upNumber two, never let ’em know your next move
Don’t you know Bad Boys move in silence or violence
Take it from your highness
I done squeezed mad clips at these cats for they bricks and chipsNumber three, never trust nobody
Your moms’ll set that *** up, properly gassed up
Hoodie to mask up, s***, for that fast buck
She be layin’ in the bushes to light that *** upNumber four, know you heard this before
Never get high on your own supplyNumber five, never sell no *** where you rest at
I don’t care if they want a ounce, tell ’em bounceNumber six, that God*** credit, dig it
You think a *** head payin’ you back, *** forget itSeven, this rule is so underrated
Keep your family and business completely separated
Money and blood don’t mix like two *** and no ***
Find yourself in serious s***Number eight, never keep no weight on you
Them cats that squeeze your *** can hold jobs tooNumber nine, shoulda been number one to me
If you ain’t gettin’ bags stay the f*** from police
If niggaz think you snitchin’ ain’t tryin’ listen
They be sittin’ in your kitchen, waitin’ to start hittin’Number ten, a strong word called consignment
Strictly for live men, not for freshmen
If you ain’t got the clientele say hell no
‘Cause they gon’ want they money rain, sleet, hail, snowDon’t forget the admonition from Notorious B.IG. gives that should never be diminished:
Follow these rules, you’ll have mad bread to break up
If not, twenty-four years, on the wake up
Slug hit your temple, watch your frame shake up
Caretaker did your makeup, when you pass
An information security professional known as “The Grugq” gave a very interesting talk on OPSEC, I think it is worth taking a glance at (try to contain all laughter and bafoonery at the preview image – we’re running a family show here, folks):
- « Previous Page
- 1
- …
- 8
- 9
- 10
- 11
- 12
- …
- 15
- Next Page »